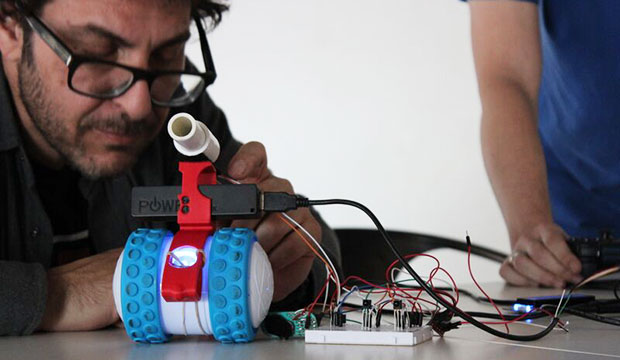
Canonical last week announced plans to launch the Internet of Toys, an open source initiative calling on toy makers, hackers, Internet of Things fans and innovators to build the next generation of Web-accessing toys.
The company is partnering with the Hybrid Group and Erle Robotics for the initiative.
Participants will build the next generation of toys around open source tools such as Cylon JS, Gobot, Snappy Ubuntu Core, Snapcraft, ROS and Erle-Spider.
“The idea is that any toy, for kids and not-so-kids, can be app-enabled and have an app store and, potentially, peripherals,” said Maarten Ectors, a vice president at Canonical.
For example, toys released in conjunction with movies could have a speaker and a microphone and let users communicate through Facebook.
That vision raises questions of privacy and security. There are no security standards for IoT devices, and baby monitors, smart cars and medical devices have been hacked.
“That’s why manufacturers should change from embedded, do-your-own Linux and microcontroller solutions that don’t focus on security and transactional updates to Snappy Ubuntu Core,” Ectors told LinuxInsider. “Ubuntu Core assumes apps are hostile to other apps and the operating system.”
About Snappy Ubuntu Core
Snappy Ubuntu Core offers a minimal server image with the same libraries as traditional Ubuntu, but it — and Snappy apps — can be updated transactionally and rolled back if necessary.
Snappy Ubuntu runs on any device with an ARMv7 or Intel x86 processor and at least 256 MB of RAM.
Being able to update the system transactionally “means that security patches can be continuously applied without breaking the device,” Ectors explained.
IoT’s Lack of Security
Rapid7 last month disclosed that baby monitors are riddled with security vulnerabilities.
Security flaws previously were discovered in several of the devices listed.
Modern automobiles are vulnerable to hacking, as demonstrated when two white-hat hackers took a Jeep Cherokee on a joyride earlier this year.
The IoT lacks security, the Online Trust Alliance warned. Only 10 of the top 50 IoT device manufacturers passed the security audit for OTA’s 2015 honor roll, 38 failed, and the last two neither failed nor made the honor roll.
The OTA has set up a working group to develop a framework of best practices for IoT device manufacturers and retailers.
“A common set of best practices is really the only way to go forward for security in the Internet of Things,” said Tim Erlin, director of IT security and risk strategy at Tripwire.
“As more devices are able to interact with the physical world around us, cybersecurity really becomes an issue of cybersafety,” he told LinuxInsider. “If we don’t address the logical security in the IoT soon, we’ll end up with a consumer safety requirement to manage.”
However, the framework must be backed up by some form of economic coercion, Erlin contended. “If the goal is safety, it must be much more expensive to be unsafe than compliant.”
Making Your IoT Toy Safe
Hackers might be able to eavesdrop on a family’s interactions by breaking into a toy connected to the Internet. A connection through a central server in a smart home opens the possibilities for mischief.
“Most WiFi points used in homes and businesses today and purchased five years ago are still running the same firmware as when they were first plugged in,” Ectors said. “This means they have Heartbleed, Shellshock and many other serious security flaws.”
Toys built around Snappy Ubuntu Core might be safe because “Ubuntu Core assumes devices will have to be continuously updated when security holes are discovered,” he remarked. Snappy Ubuntu Core “takes security very seriously by containing apps; mounting the operating system in read-only mode; and secure boot, disk encryption.”